Cyber Security | Ethical Hacking | Pentesting Lab | Vulnhub | breakout II
Cyber Security | Ethical Hacking | Pentesting Lab | Vulnhub | breakout II
Cyber Security | Ethical Hacking | Pentesting Lab | Vulnhub | breakout I
Cyber Security | Ethical Hacking | Pentesting Lab | Vulnhub |Thales1 partie I
Methodology:
Network scanning
netdiscover
nmap
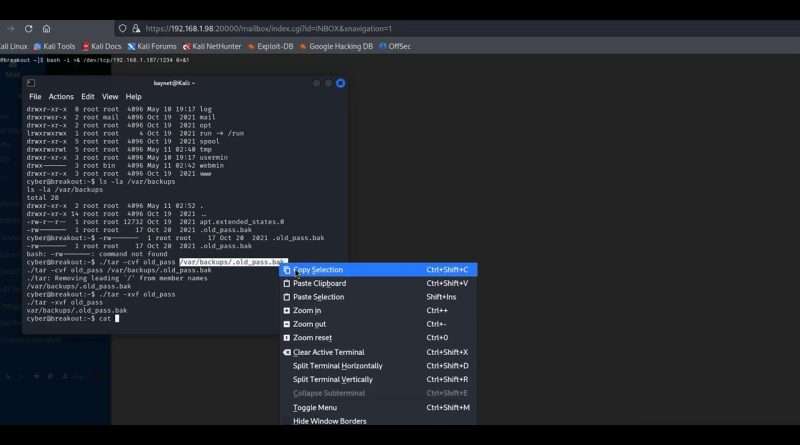
Enumeration
Abusing HTTP
Exploitation
Capture the Flag
Cyber Security | Ethical Hacking | Pentesting Lab | Vulnhub |The Planets: Earth partie 1
• Cyber Security | Ethical Hacking | Pe…
Cyber Security | Ethical Hacking | Pentesting Lab | Vulnhub | BsidesVancouver2018
• Cyber Security | Ethical Hacking | Pe…
Pentesting Lab Exercises Series-Vulnhub Virtual Machine Name: pylington:1
• Cyber Security | Ethical Hacking | Pe…
1. #Hyper-A
2. #ethicalhacking
3. #FindPopularWebMachineTags
4. #WebHackingN7
5. #HackingTutorials
6. #cybersecuritytips
7. #websecurity
8. #PopularHackingTechniques
9. #WebVulnerabilities
10. #HackingToolsandMethods
11. #learnethicalhacking
12. #WebExploitation
13. #cyberdefense
14. #networksecurity
15. #webapplicationsecurity
16. #HackingResources
17. #ethicalhackingforbeginners
18. #cybersecurityeducation
19. #WebMachineN7
20. #WebHackingStrategies
Views : 2
cyber security
Source by Kay Cybersecurity & Mathématiques