Deploying Cisco ASA and Other Firewalls for Network Engineers (Preview)
More details at: http://www.routehub.net/firewalls
Format: Workbook
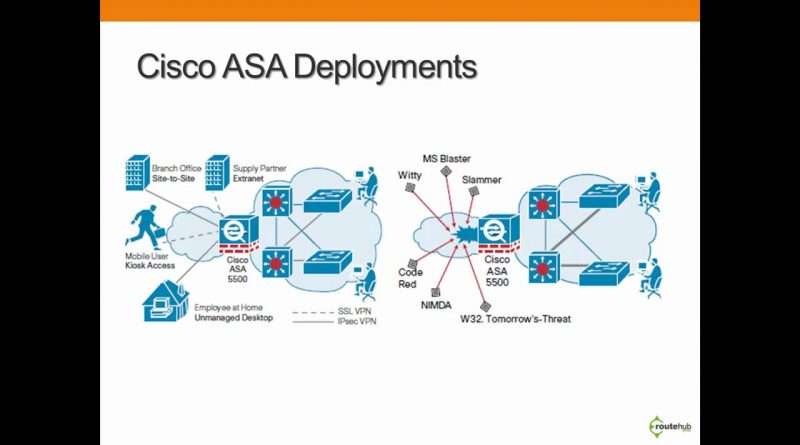
Learn how to deploy the following for the Cisco ASA
* Base Configuration
* Device Access (SSH, Telnet)
* NAT (Static, PAT, NAT Port Redirect)
* HTTP and ASDM
* ASA Image
* Stateful Firewall
* DHCP Server
* OSPF Routing
* PPPoE
* LDAP intergration with Active Directory for Remote Access
* Remote Access: SSL VPN (Tunnel Mode/SVC)
* Remote Access: Client IPSec VPN
* Remote Access: L2TP over IPSec
* Site-Based VPN without Remote Access
* Site-Based VPN with Remote Access
* IP SLA with Dual ISP
* Rate Limiting (Policing)
* Active/Passive Failover
* Troubleshooting Cases
Other Cisco Solution Deployments include:
* Cisco PIX: Remote Access using Client IPSec VPN
* Cisco PIX: PPTP (VPDN)
* Cisco PIX: Active/Passive Failover
* Cisco PIX: Authentication Proxy
* Cisco FWSM for Catalyst 6500 Series
* Cisco ACL: Guest/DMZ ACL Policy
* Cisco ACL: Outbound ACL Policy
* Cisco ACL: RFC 1918 Filtering
* Cisco IOS Firewall: Reflexive ACL
* Cisco IOS Firewall: Context-Based Access Control (CBAC)
* Time-Based ACL
Firewall Equipment List:
* Cisco ASA 5500 Series (ASA 5505, ASA 5510)
* Cisco PIX 500 Series (PIX 515)
* Cisco IOS Routers: CIsco ISR 800, Cisco ISR 2800
* Cisco Firewall Services Module (FWSM) for Cisco Catalyst 6500 Series
Views : 22921
network engineer